ZetaChain Exploit Was Preventable: The Bug Was Reported and Dismissed Before the Attack
-
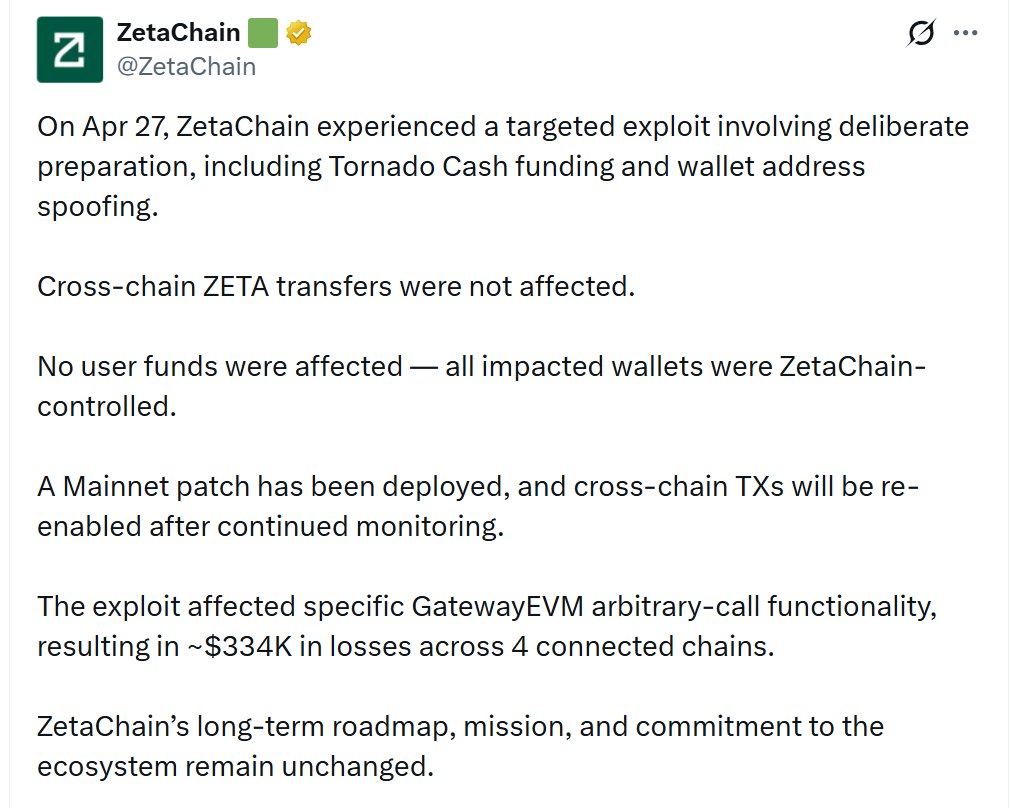
ZetaChain's post-mortem of its $334,000 exploit has revealed an uncomfortable detail: the vulnerability that enabled the attack had already been flagged through the protocol's own bug bounty program before it was used against the network. The team acknowledged in its post-mortem that the submission was dismissed as intended behavior rather than investigated as a genuine risk, a decision that directly contributed to the exploit occurring. The admission has drawn sharp criticism from the security research community, with one researcher noting that bug bounty programs at many DeFi protocols effectively create a perverse incentive structure by failing to compensate researchers for real discoveries while leaving vulnerabilities in place for attackers to exploit.The attack itself was not opportunistic. ZetaChain's post-mortem reveals the attacker funded their wallet through Tornado Cash three days before the exploit, deployed a purpose-built drainer contract on ZetaChain, and ran an address poisoning campaign before executing the attack across nine transactions on four chains including Ethereum, Arbitrum, Base, and BSC.
The exploit combined three individually minor design flaws: the gateway allowed unrestricted arbitrary cross-chain instructions, the receiving end would execute almost any command on any contract with a blocklist too narrow to catch basic token transfer functions, and wallets that had previously used the gateway had left unlimited spending permissions in place that were never cleaned up. By chaining all three, the attacker instructed the gateway to transfer tokens from victim wallets to their own address, and the gateway complied. No user funds were affected, but the incident has prompted ZetaChain to review how it handles bug bounty submissions involving chained attack vectors that appear harmless in isolation but dangerous in combination.





















