North Korea-Linked Lazarus Group Spreads “Mach-O Man” macOS Malware in Crypto Attacks
-
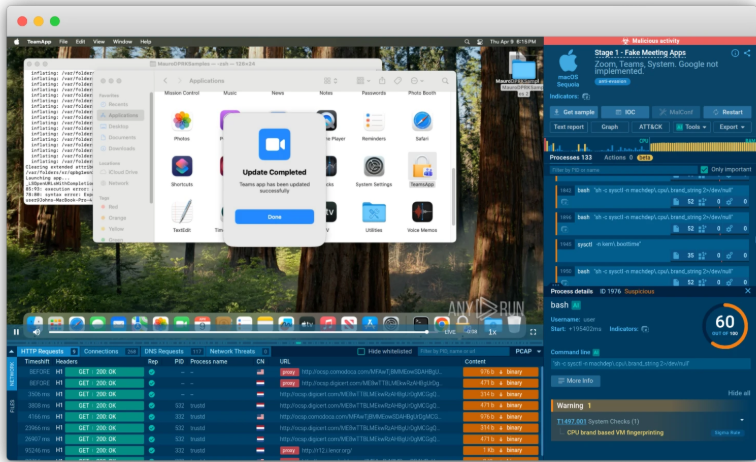
Fake Mach-O Man Kit apps. Source: ANY.RUNSecurity researchers have uncovered a new macOS malware campaign tied to the Lazarus Group, the cybercrime operation widely blamed for some of the largest crypto thefts in history. The newly identified “Mach-O Man” malware kit is being distributed through social engineering schemes that impersonate Zoom or Google Meet calls to trick victims into executing malicious commands.
Once installed, the malware quietly downloads in the background, bypassing traditional security controls. It can then extract browser credentials, cookies, password data, and macOS Keychain information, giving attackers deep access to both personal and corporate systems.
Researchers say the stolen data is compressed and exfiltrated via Telegram before the malware deletes itself to avoid detection. The campaign highlights how Lazarus Group continues expanding beyond crypto-native targets into broader enterprise environments.





















