North Korea’s Crypto Strategy Expands Beyond Hacks
-
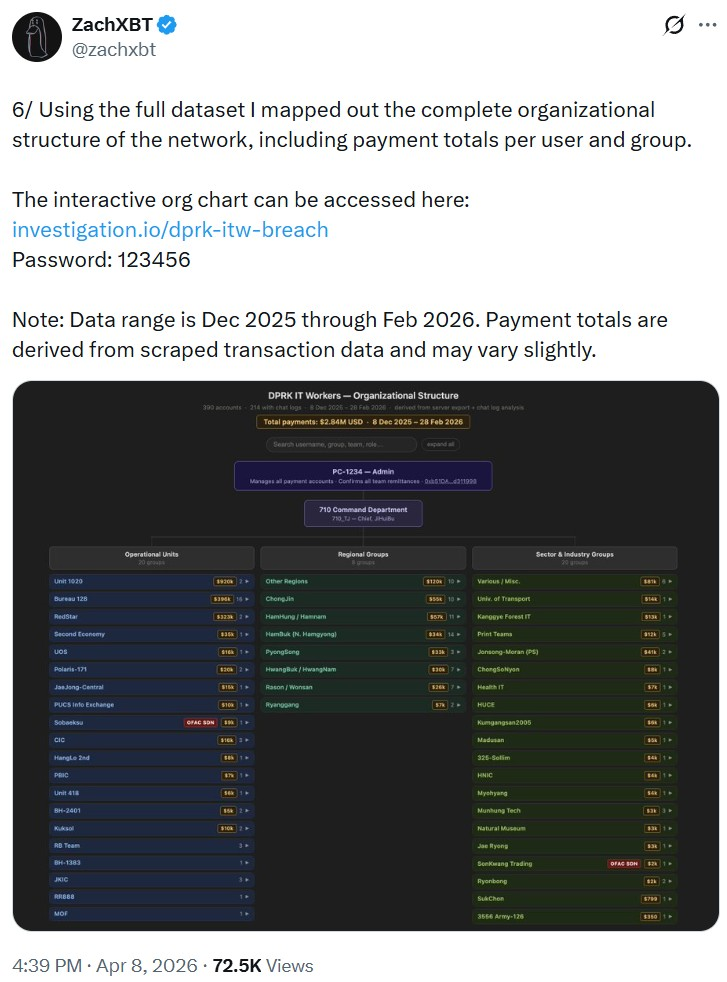
Beyond large-scale exploits like Drift and Bybit, North Korea is running a broader strategy to generate crypto revenue. Investigations revealed networks of fake developers infiltrating companies, earning salaries and funneling funds back through coordinated systems.
These operatives use falsified identities, remote access setups, and even basic infrastructure (like shared platforms with weak security) to operate at scale. Combined with high-profile hacks, this creates a dual strategy: short-term theft and long-term infiltration, making North Korea one of the most persistent threats to the global crypto ecosystem.
-
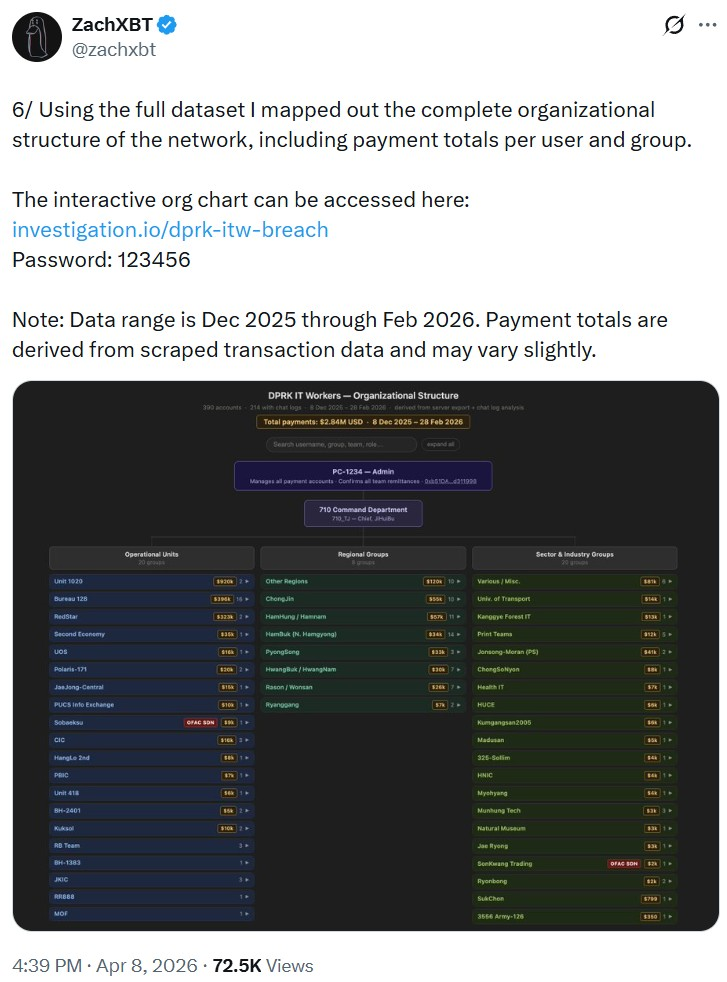
Beyond large-scale exploits like Drift and Bybit, North Korea is running a broader strategy to generate crypto revenue. Investigations revealed networks of fake developers infiltrating companies, earning salaries and funneling funds back through coordinated systems.
These operatives use falsified identities, remote access setups, and even basic infrastructure (like shared platforms with weak security) to operate at scale. Combined with high-profile hacks, this creates a dual strategy: short-term theft and long-term infiltration, making North Korea one of the most persistent threats to the global crypto ecosystem.
@tradelikepro this dual strategy of hacks + infiltration is actually pretty effective from a long-term perspective





















